- Company
- Product
- Resources
- Solutions
- Request a Demo
April 2, 2026
How can you detect malicious or anomalous activity at the edge of your network, when your environment includes a pipeline...
March 26, 2026
PCAPs (packet captures) are invaluable information sources for identifying assets and activities on a network. We’ve talked...
March 18, 2026
If you’re a technologist, especially if you’re coming from IT into OT, you probably already know your way around...
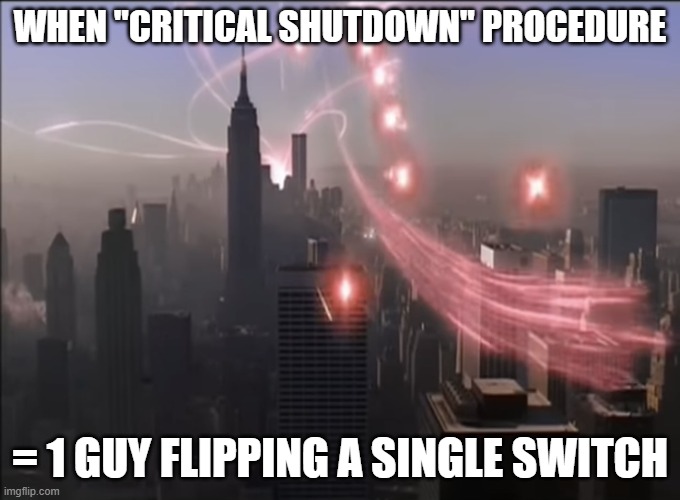
March 12, 2026
If you’re an OT operator or defender, some of the most beloved movies of all time can seem like horror flicks. Not...
February 23, 2026
There’s an OT network security dashboard somewhere right now with over 10,000 alerts on it. And nobody is looking at it....
February 20, 2026
[This is the third blog in our series “IT Org Now OT Curious,” examining the differences between IT and OT cybersecurity....
February 12, 2026
[This is the second blog in our series focused on IT orgs that are now OT curious, where we examine the differences between...
February 6, 2026
If you’ve spent years securing enterprise IT environments and recently found yourself “OT curious,” welcome....
January 23, 2026
If you work in OT, humor isn’t optional… It’s a survival skill. And like all cybersecurity fields, the memes sometimes...
January 16, 2026
As many operators already know, open source software is becoming more common in Operational Technology (OT) and Industrial...